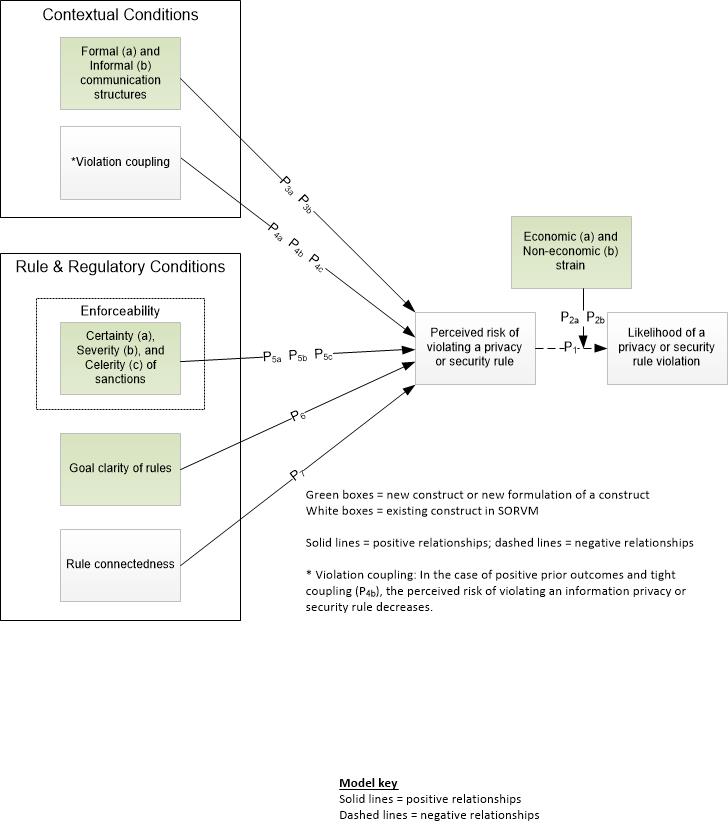
Selective organizational information privacy and security violations model (SOIPSVM)
Acronym
SOIPSVM
Alternate name(s)
n/a
Main dependent construct(s)/factor(s)
Likelihood of a privacy or security rule violation [by the organization]
Main independent construct(s)/factor(s)
Contextual conditions of formal and informal communication structures, and coupling between violation and outcomes. Rule characteristics of enforceability through certainty, severity, and celerity of sanctions; goal clarity of rules, and rule connectedness, perceived risk of violating a privacy or security rule, economic strain, and non-economic strain.
Motivation for SOIPSVM / Why IS researchers can benefit from using it
Motivation for creation of the theory: Privacy and security concerns are pervasive because of the ease of access to information. Recurrent negative cases in the popular press attest to the failure of current privacy regulations to keep consumer and protected health information sufficiently secure in today’s climate of increased IT use. One reason for such failure is that organizations violate these regulations for multiple reasons. To address this issue, Wall, Lowry, and Barlow (2016) proposed a theoretical model to explain the likelihood that organizations will select an externally governed privacy or security rule for violation in response to organizational strain or slack resources. This proposed theoretical model, is the selective organizational information privacy and security violations model (SOIPSVM).
Concise description of theory
The selective organizational information privacy and security violations model (SOIPSVM), explains how organizational structures and processes, along with characteristics of regulatory rules, alter perceptions of risk when an organization’s performance does not match its aspiration levels and, thereby, affects the likelihood of rule violations. Importantly, SOIPSVM is contextualized for the domain of organizational privacy and security violations. SOIPSVM builds on and extends the selective organizational rule violations model (SORVM), which posits that organizational rule violations are selective. SOIPSVM provides at least four contributions to the privacy and security literature that can further guide empirical research and practice. First, SOIPSVM introduces the concept of selectivity in rule violations to privacy and security research. This concept can improve privacy and security research by showing that organizational violations of privacy and security rules are dynamic and selective yet influenced by external forces. Second, SOIPSVM extends the boundaries of SORVM, which is limited to explaining the behavior of organizations under strain, such as economic hardship. SOIPSVM contributes to the theory of selective deviance by proposing that selectivity extends to organizations with slack resources. Third, SOIPSVM addresses ideas of non-economic risk and strain in addition to economic risk and strain. Thus, SOIPSVM explains organizational rule-violating behavior as an attempt to protect core organizational values from external entities that pressure organizations to change their values to comply with rules. Fourth, SOIPSVM broadens the theoretical scope of two important constructs (namely, structural secrecy and procedural emphasis) to improve the model’s explanatory power. Fifth, SOIPSVM identifies important elements of rule enforcement by drawing from the tenets of general deterrence theory.
Diagram/schematic of theory
Figure 1. Overview of the selective organizational information privacy and security violations model (SOIPSVM), from Wall, Lowry, and Barlow (2016).
Originating author(s)
Jeffrey D. Wall, Paul Benjamin Lowry, and Jordan B. Barlow
Seminal articles
Jeffrey D. Wall, Paul Benjamin Lowry, and Jordan Barlow (2016). “Organizational violations of externally governed privacy and security rules: Explaining and predicting selective violations under conditions of strain and excess,” Journal of the Association for Information Systems (JAIS), vol. 17(1), pp. 39-76 (http://aisel.aisnet.org/jais/vol17/iss1/).
Originating area
Information systems (native theory)
Level of analysis
Organization
IS and non-IS articles that use the theory
TBD
Links from this theory to other theories
GDT or General_deterrence_theory
External links
n/a