Protection motivation theory
Acronym
PMT
Alternate name(s)
n/a
Main dependent construct(s)/factor(s)
Protection motivation “the protection motivation concept involves any threat for which there is an effective recommended response that can be carried out by the individual” (Floyd et al. 2000, p. 409).
Main independent construct(s)/factor(s)
Fear, fear appeal, threat severity, threat susceptibility, self-efficacy, response efficacy, response costs, maladaptive intrinsic rewards, maladaptive extrinsic rewards, threat appraisal, coping appraisal, adaptive response, maladaptive response
Concise description of theory
PMT’s main contribution is its capacity to predict users’ intentions to protect themselves after receiving fear-arousing recommendations: “The purpose of PMT research is usually to persuade people to follow the communicator’s recommendations; so, intentions indicate the effectiveness of the attempted persuasion” (Floyd et al. 2000, p. 411).
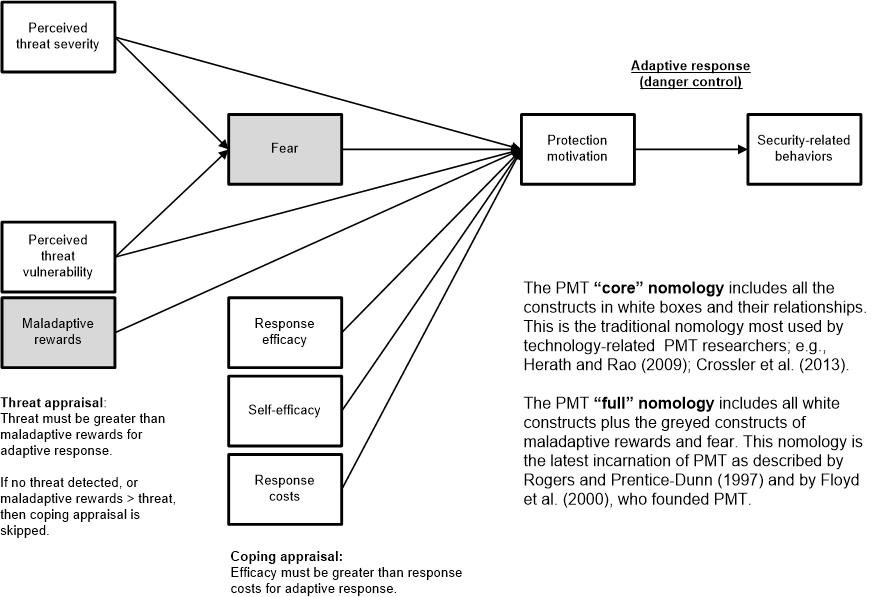
As explained carefully by Boss et al. (2015) and Posey et al. (2015), threat appraisal and coping appraisal, the two components of PMT shown in Figure 1 (as a process variance model) that shape protection intentions, form the core assumptions of PMT. The basic idea of PMT is that a fear appeal triggers the threat-appraisal process. Two processes and outcomes must occur for a person to engage in an adaptive response: First, in the threat-appraisal process, the threat and generated fear that inspire protection motivation must be weighted more heavily than maladaptive rewards earned by not engaging in protection motivation.
Second, in the coping-appraisal process, a person’s response efficacy and self-efficacy must outweigh the response costs for engaging in the protection motivation. In terms of threat appraisal, it is important to emphasize that the feeling of fear is conceptually distinct from the fear appeal or fear-appeal message. In a PMT context, fear is defined as a “relational construct, aroused in response to a situation that is judged as dangerous and toward which protective action is taken” (Rogers 1975, p. 96). Separately, a fear appeal is the stimulus designed to trigger both fear and the threat-appraisal and coping-appraisal processes. Ideally a fear appeal does not just increase threat but would also increase efficacy by giving a respondent a path to address the threat. Importantly, the best fear appeals create both high threat and high efficacy because they address both the threat and the individual’s ability to deal with it (Milne et al. 2000; Witte and Allen 2000). The fear-appeals literature uses the message (fear appeal) as a manipulation.
Diagram/schematic of theory
Figure 1. Overview of the Core and Full Nomologies of PMT as Process Variance Model from Boss et. al. (2015, p. 840)
Originating author(s)
R. W. Rogers; later revised with S. Prentice-Dunn
Seminal articles
Rogers, R. W. 1975. "A Protection Motivation Theory of Fear Appeals and Attitude Change," Journal of Psychology (91:1), pp. 93-114.
Rogers, R. W. 1983. "Cognitive and Physiological Processes in Fear Appeals and Attitude Change: A Revised Theory of Protection Motivation," in Social Psychophysiology: A Sourcebook, J. T. Cacioppo, and R. E. Petty (eds.), New York, NY: Guilford, pp. 153-176.
Rogers, R. W., and Prentice-Dunn, S. 1997. "Protection Motivation Theory," in Handbook of Health Behavior Research I: Personal and Social Determinants, D. S. Gochman (ed.), New York, NY: Plenum Press, pp. 113-132.
Floyd, D. L., Prentice-Dunn, S., and Rogers, R. W. 2000. "A Meta-Analysis of Research on Protection Motivation Theory," Journal of Applied Social Psychology (30:2), pp. 407-429.
Leading IS Articles that Contextualized PMT to IS context
Johnston, A. C., and Warkentin, M. 2010. "Fear Appeals and Information Security Behaviors: An Empirical Study," MIS Quarterly (34:1), pp. 549-566
This article re-introduced the idea of the fear appeal from PMT to the IS field.
Johnston, A. C., Warkentin, M., and Siponen, M. 2015. "An Enhanced Fear Appeal Rhetorical Framework: Leveraging Threats to the Human Asset through Sanctioning Rhetoric," MIS Quarterly (39:1), pp. 113-134.
This article shows how sanctioning rhetoric can improve the effectiveness of fear-appeal manipulations.
Scott R. Boss, Dennis F. Galletta, Paul Benjamin Lowry, Gregory D. Moody, and Peter Polak (2015). “What do users have to fear? Using fear appeals to engender threats and fear that motivate protective behaviors in users,” MIS Quarterly (MISQ), vol. 39 (4), pp. 837–864.
This article returns the IS field to the full nomology of PMT and shows how to use it properly for manipulated fear appeals with the full nomology, including the measurement of fear.
Clay Posey, Tom L. Roberts, and Paul Benjamin Lowry (2015). “The impact of organizational commitment on insiders’ motivation to protect organizational information assets,” Journal of Management Information Systems (JMIS) (forthcoming).
This article shows how to best use the full PMT nomology with organizational commitment in a non-manipulated fear appeal general threat context to increase ISP compliance
Originating area
Health communication and social psychology
Level of analysis
Individual
IS articles that use the theory
Anderson, C. L., and Agarwal, R. 2010. "Practicing Safe Computing: A Multimethod Empirical Examination of Home Computer User Security Behavioral Intentions," MIS Quarterly (34:3), pp. 613-643.
Scott R. Boss, Dennis F. Galletta, Paul Benjamin Lowry, Gregory D. Moody, and Peter Polak (2015). “What do users have to fear? Using fear appeals to engender threats and fear that motivate protective behaviors in users,” MIS Quarterly (MISQ), vol. 39 (4), pp. 837–864
Claar, C. L., and Johnson, J. 2012. "Analyzing Home PC Security Adoption Behavior," Journal of Computer Information Systems (52:4), pp. 20-29.
Crossler, R. E., and Bélanger, F. 2014. "An Extended Perspective on Individual Security Behaviors: Protection Motivation Theory and a Unified Security Practices (USP) Instrument," DATA BASE for Advances in Information Systems (45:4), pp. 51-71.
Gurung, A., Luo, X., and Liao, Q. 2009. "Consumer Motivations in Taking Action against Spyware: An Empirical Investigation," Information Management & Computer Security (17:3), pp. 276-289.
Herath, T., and Rao, H. 2009. "Protection Motivation and Deterrence: A Framework for Security Policy Compliance in Organisations," European Journal of Information Systems (18:2), pp. 106-125.
Herath, T., Chen, R., Wang, J., Banjara, K., Wilbur, J., and Rao, H. R. 2012. "Security Services as Coping Mechanisms: An Investigation into User Intention to Adopt an Email Authentication Service," Information Systems Journal (24:1), pp. 61-84.
Ifinedo, P. 2012. "Understanding Information Systems Security Policy Compliance: An Integration of the Theory of Planned Behavior and the Protection Motivation Theory," Computers & Security (31:1), pp. 83-95.
Jenkins, J. L., Grimes, M., Proudfoot, J., and Lowry, P. B. 2013. "[http://papers.ssrn.com/sol3/papers.cfm?abstract_id=2292761 Improving password cybersecurity through inexpensive and minimally invasive means: Detecting and deterring password reuse through keystroke-dynamics monitoring and just-in-time warnings]," Information Technology for Development (20:2), pp. 196-213.
Johnston, A. C., and Warkentin, M. 2010. "Fear Appeals and Information Security Behaviors: An Empirical Study," MIS Quarterly (34:1), pp. 549-566.
Johnston, A. C., Warkentin, M., and Siponen, M. 2015. "An Enhanced Fear Appeal Rhetorical Framework: Leveraging Threats to the Human Asset through Sanctioning Rhetoric," MIS Quarterly (39:1), pp. 113-134.
Lai, F., Li, D., and Hsieh, C.-T. 2012. "Fighting Identity Theft: The Coping Perspective," Decision Support Systems (52:2), pp. 353-363.
LaRose, R., Rifon, N. J., and Enbody, R. 2008. "Promoting Personal Responsibility for Internet Safety," Communications of the ACM (51:3), pp. 71-76.
Lee, D., Larose, R., and Rifon, N. 2008. "Keeping Our Network Safe: A Model of Online Protection Behaviour," Behaviour & Information Technology (27:5), pp. 445-454.
Lee, Y., and Larsen, K. R. 2009. "Threat or Coping Appraisal: Determinants of SMB Executives' Decision to Adopt Anti-Malware Software," European Journal of Information Systems (18:2), pp. 177-187
Lee, Y. 2011. "Understanding Anti-Plagiarism Software Adoption: An Extended Protection Motivation Theory Perspective," Decision Support Systems (50:2), pp. 361-369.
Liang, H., and Xue, Y. 2010. "Understanding Security Behaviors in Personal Computer Usage: A Threat Avoidance Perspective," Journal of the Association for Information Systems (11:7), pp. 394-413.
Clay Posey, Tom L. Roberts, Paul Benjamin Lowry, James Courtney, and Rebecca J. Bennett (2011). “Motivating the insider to protect organizational information assets: Evidence from protection motivation theory and rival explanations,” Proceedings of the Dewald Roode Workshop in Information Systems Security 2011, IFIP WG 8.11 / 11.13, Blacksburg, VA, September 22–23, pp. 1–51.
Clay Posey, Tom L. Roberts, and Paul Benjamin Lowry (2015). “The impact of organizational commitment on insiders’ motivation to protect organizational information assets,” Journal of Management Information Systems (JMIS) (forthcoming).
Links from this theory to other theories
n/a
External links
n/a