Prospect theory

Prospect theory
Acronym
PT
Alternate name(s)
N/A
Main dependent construct(s)/factor(s)
1. Escalation of commitment to IT projects
2. Software completion time and budgets
3. Technology investment decisions
4. Software project bidding price
5. iPrice – Information goods pricing
6. Online bidder satisfaction
Main independent construct(s)/factor(s)
1. Sunk cost
2. Risk Preference of decision maker/evaluator (averse or seeking)
3. Decision domain (gain or loss)
4. Project size
5. Presence or absence of an alternative course of action
6. Price
7. Hedonic value
8. Psychological determinants of decision maker
9. Social determinants of group surrounding decision maker
10. Project determinants
11. Structural determinants of environment
Concise description of theory
Prospect theory is utilized to make decisions that involve risks or gambles. This theory was developed in 1979 as a solution to the shortfalls and contradictions that were found in expected utility theory in certain situations. One of the most significant aspects of prospect theory is the suggestion that individuals avoid risk when they perceive their current prospects or situation to be positive (a gain decision domain), and individuals seek risk when they perceive the current prospects or situation to be negative (a loss decision domain). Additionally, the theory shows that individuals make decisions based on shifts in wealth versus total wealth itself. This shift in wealth becomes the reference point from where any new decisions are made.
In prospect theory, risky decisions (prospects) are segregated into two phases: editing and evaluation. In the editing phase, individuals start coding an offered prospect by defining gains and losses in relation to a reference point. Next, prospects with identical outcomes are combined; then the riskless component of the prospect is segregated; and finally, common components of each prospect are cancelled. In the second phase, the prospect is evaluated. This evaluation uses statistical analysis to measure and compare risky prospects. Prospect theory introduces two indices that are used in this comparison of the prospects: the utility (or value) function and the decision weighting function. The use of the two functions is what differentiates prospect theory from expected utility theory.
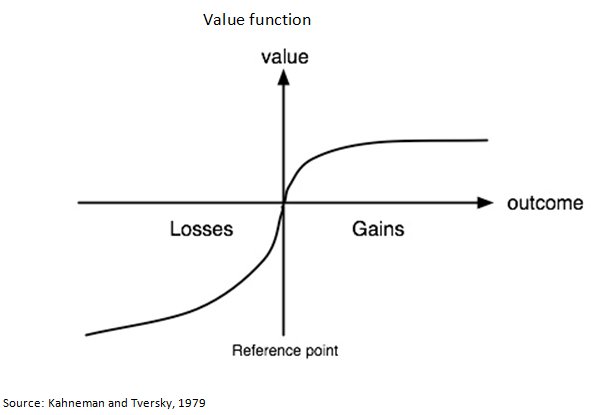
The value function (shown below) was developed to show how either a gain or loss decision domain affects a risky decision. This value function is S-shaped: concave above the reference point and convex below it. It can be best explained using the following example: the value of a $10 difference between two prospective payoffs depends on whether they fall on the low or high end of the value function. The theory suggests that the $10 difference in a payoff is valued more on the low end of the curve ($10 versus $20 payoff) than it is on the upper end of the curve ($500 versus $510 payoff). The same relationship holds true for losses, except that the value lost is more extreme in the loss quadrant versus value gained in the gain quadrant when the same dollar amounts are considered.
Diagram/schematic of theory
Originating author(s)
Prospect theory was developed by Daniel Kahneman and Amos Tversky in 1979 as an alternative to expected utility theory.
Seminal articles
Kahneman, D., and A. Tversky. 1984. "Choices, Values, and Frames," American Psychologist (39:4), 04, pp. 341-350.
———. 1979. "Prospect Theory: An Analysis of Decision Under Risk," Econometrica (47:2), 03, pp. 263-291.
Tversky, A., and D. Kahneman. 1981. "The Framing of Decisions and the Psychology of Choice," Science (211:4481), 01, pp. 453-458.
Additional Seminal articles that initially applied Prospect Theory to escalation of commitment and sunk cost, which have been used as the basis for some IS research.
Bazerman, M. H. 1984. "The Relevance of Kahneman and Tversky's Concept of Framing to Organizational Behavior," Journal of Management (10:3), Fall, pp. 333-343.
Garland, H., and S. Newport. 1991. "Effect of Absolute and Relative Sunk Costs on the Decision to Persist with a Course of Action," Organizational Behavior & Human Decision Processes (48:1), 02, pp. 55.
Whyte, G. 1986. "Escalating Commitment to a Course of Action: A Reinterpretation," Academy of Management Review (11:2), 04, pp. 311-321.
Originating area
Psychology
Level of analysis
Individual, Group, Organization, Inter-organizational
IS articles that use the theory
Jørgensen, M., and G. J. Carelius. 2004. "An Empirical Study of Software Project Bidding," IEEE Transactions on Software Engineering (30:12), 12, pp. 953-969.
Keil, M., J. Mann, and A. Rai. 2000. "Why Software Projects Escalate: An Empirical Analysis and Test of Four Theoretical Models," MIS Quarterly (24:4), 12, pp. 631-664.
Keil, M., R. Mixon, T. Saarinen, and V. Tuunainen. 1994. "Understanding Runaway Information Technology Projects: Results from an International Research Program Based on Escalation Theory," Journal of Management Information Systems (11:3), Winter, pp. 65-85.
Keil, M., B. C. Y. Tan, K. Wei, T. Saarinen, V. Tuunainen, and A. Wassenaar. 2000. "A Cross-Cultural Study on Escalation of Commitment Behavior in Software Projects," MIS Quarterly (24:2), 06, pp. 299-325.
Lauer, T. W. 1996. "Software Project Managers' Risk Preferences," Journal of Information Technology (Routledge, Ltd.) (11:4), 12, pp. 287.
Newman, M., and R. Sabherwal. 1996. "Determinants of Commitment to Information Systems Development: A Longitudinal Investigation," MIS Quarterly (20:1), 03, pp. 23-54.
Rose, J. M., A. M. Rose, and C. S. Norman. 2004. "The Evaluation of Risky Information Technology Investment Decisions," Journal of Information Systems (18:1), Spring, pp. 53-66.
Tiwana, A., M. Keil, and R. G. Fichman. 2006. "Information Systems Project Continuation in Escalation Situations: A Real Options Model," Decision Sciences (37:3), 08, pp. 357-391.
Wu, W., B. Lin, and C. Cheng. 2009. "Evaluating Online Auction Stratagy: A Theoretical Model and Empirical Exploration," The Journal of Computer Information Systems (49:3), pp. 22-30.
Links from this theory to other theories
Expected utility theory, expectancy theory, regret theory, self-justification theory
External links
Original Contributor(s)
Jeff Reinking, University of Central Florida
Please feel free to make modifications to this site. In order to do so, you must register.
Return to Theories Used in IS Research